Part 5: Smart Contracts + AI Agents: Autonomous Systems
📚 Series Navigation
👉 Part 1: AI, Blockchain, and Cloud: Who Actually Does What?
👉 Part 2: Why Fully Decentralized AI Is (Mostly) a Myth
👉 Part 3: Web3 Data -> Cloud ML Pipelines (Spark in Practice)
👉 Part 4: AI for Blockchain Fraud & Anomaly Detection
👉 Part 5: Smart Contracts + AI Agents: Autonomous Systems
👉 Part 6: Auditable AI: Using Blockchain for Trust & Governance
Smart Contracts + AI Agents: Autonomous Systems
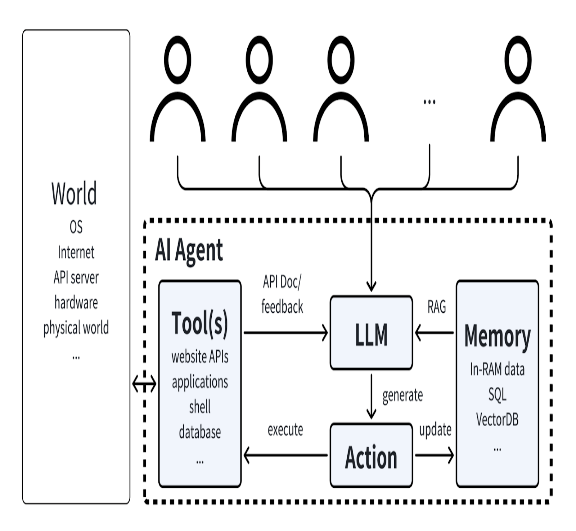
Smart contracts are deterministic enforcement engines. AI agents are adaptive decision engines. Combine them safely by treating agent output as untrusted input and enforcing guardrails on-chain. The chain should enforce invariants, not run the model.
🧩 Case Study: Autonomous Rebalancing With Hard Caps
An AI agent proposes rebalances off-chain. On-chain contracts enforce max exposure, max daily turnover, and an emergency pause. The guardrails keep failure modes bounded even when the model is wrong.
Architecture patterns
Proposal → Validate → Execute
- Agent proposes an action (signed payload)
- Contract validates caps/allowlists/thresholds
- Contract executes and emits audit events
Oracle / attestation pattern
Contracts accept signed risk attestations from authorized signers and enforce freshness windows + nonces. This keeps decisions off-chain while preserving accountability.
Guardrails (Solidity)
Exposure caps + risk threshold (baseline)
| |
Rate limiting (prevent fast mistakes)
| |
Circuit breaker / emergency pause
| |
Failure modes and mitigations
| Failure mode | Mitigation |
|---|---|
| Malicious/incorrect agent output | caps, allowlists, staged rollout |
| Oracle compromise | multiple oracles, medianization, bounds checks |
| Front-running / MEV | TWAP, slippage caps, commit-reveal |
| Reorgs / finality | confirm-finality thresholds, idempotent ops |
| Replay attacks | nonce + expiry + domain separation |
Governance patterns
- Multisig guardian for emergency pause and parameter updates
- DAO voting for policy-level changes (caps, allowlists, signer sets)
- Timelocks for upgrades
Governance is the safety net that turns an agent into a controlled system.
✅ Implementation Checklist
- Separate proposal (off-chain) from execution (on-chain)
- Validate caps/bounds/allowlists on-chain
- Add nonce + expiry to signed payloads
- Use rate limits, timelocks, and circuit breakers
- Emit audit events for every execution
⚖️ Tradeoffs
| Design | Pros | Cons |
|---|---|---|
| Fully autonomous | fast | risky without strong guardrails |
| Human approvals | safer | slower |
| Hybrid (recommended) | practical | more moving parts |
📚 Further Reading
- Smart contract security patterns (pause, timelock, allowlists)
- MEV/front-running mitigation writeups
- Oracle/attestation design patterns
Takeaway
Let AI propose, let contracts enforce, and let governance control parameters. The executeTrade snippet is only one guardrail pattern; production systems need caps, rate limits, attestations, and audit trails.